Network Intelligence Solutions
Intelligent Collection Management System
DPI-Based Service Gateway
Software DPI System
Embedded DPI Engine
Intelligent Application System
Data Synthesis And Content Restoration System
Big Data Platform
Internet Deep Visualization Analysis System
User Behavior Log Retention System
Internet Content Operation System
Refined Market Operation Support System
DPI-Based Service Gateway
Software DPI System
Embedded DPI Engine
Intelligent Application System
Data Synthesis And Content Restoration System
Big Data Platform
Internet Deep Visualization Analysis System
User Behavior Log Retention System
Internet Content Operation System
Refined Market Operation Support System
Information Security Protection Solutions
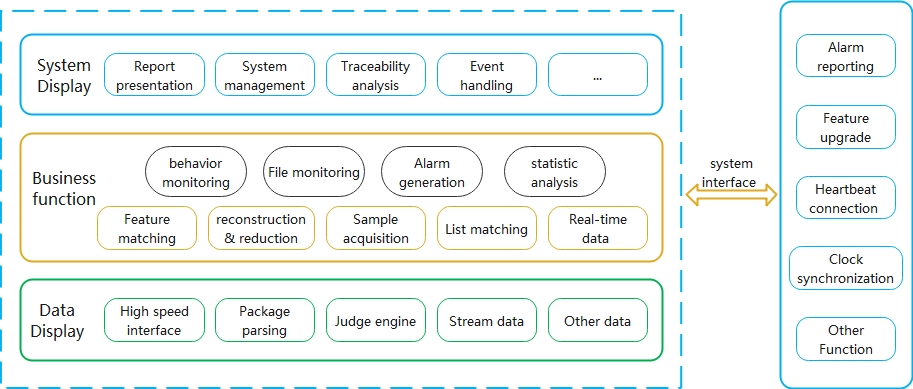
Internet Information Security Management System
IDCISP Information Security Management System
Abnormal Traffic Monitoring And Protection System
Abnormal Traffic Monitoring And Protection System
IDCISP Information Security Management System
Abnormal Traffic Monitoring And Protection System
Abnormal Traffic Monitoring And Protection System
Data Analysis
IDC Traffic Operation Analysis Service
Internet Resource Analysis and Scheduling Optimization Services
Internet Service Quality Analysis and Evaluation Services
DNS Problem Analysis and Optimization Services
IDC Traffic Operation Analysis Service
Internet Resource Analysis and Scheduling Optimization Services
Internet Service Quality Analysis and Evaluation Services
DNS Problem Analysis and Optimization Services
Support Services
System Inspection
Using proprietary inspection and maintenance tools to conduct real-time status inspections of the DPI system, monitoring the operational status, software performance, resource usage, and allocation of networks and servers in real-time.
Safety Inspection
Regularly conduct security and compliance checks, vulnerability checks on application system software and hardware, and reinforce the system's defensive capabilities on the basis of continuous monitoring services.
System Inspection
Using proprietary inspection and maintenance tools to conduct real-time status inspections of the DPI system, monitoring the operational status, software performance, resource usage, and allocation of networks and servers in real-time.
Safety Inspection
Regularly conduct security and compliance checks, vulnerability checks on application system software and hardware, and reinforce the system's defensive capabilities on the basis of continuous monitoring services.
User Response
When hardware equipment or servers fail, software and related systems run abnormally, or business interruption or operational efficiency cannot meet normal operating requirements due to reasons such as misoperation, we promptly handle problems for customers.
Data Service
When there is data deviation in the system, timely check and restore backup data to restore normal operation of the system.
- Haohan Data shines on MWC2024 to show innovation strength
- Cloud Vision Low code Intelligent Application Platform Helps Enterprises Transform Digitally
- Haohan Data was invited to participate in openEuler Summit 2023 to jointly build a new open source ecosystem
- Haohan made an in-depth appearance at the 2023 Kunpeng all-in-one machine technology application conference, and jointly released the super integrated all-in-one machine scheme for network intelligent applications
- Build together! Haohan Data, Wenjiang District Bureau of Commerce, Southwestern University of Finance and Economics, and Databank Technology China Industrial Chain Big Data Lab will work together to promote high-quality indus
- The haohan data cloud vision passed the low code advanced level certification of the ICT Academy and was unveiled at the 2023 Digital Transformation and Development Conference
 Mobile World Congres...
Mobile World Congres...
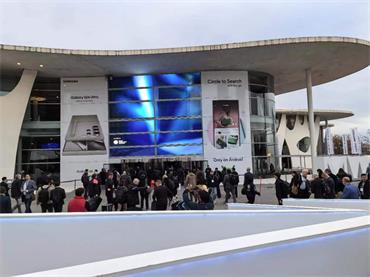 Mobile World Congres...
Mobile World Congres...
HaoHan Data
English中文